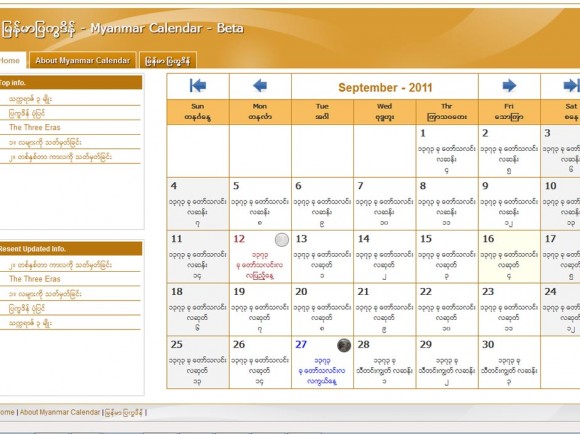
PlanetCreator‘s Security Team Researcher Infofreakzzz reported another Critical SQL injection (vulnerability) on Myanmar Calendar URL : http://www.myanmarcalendar.org/
SQL injection is a code injection technique that exploits a security vulnerability occurring in the database layer of an application. The vulnerability is present when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and thereby unexpectedly executed.
informed to :- webmaster
If you want to see detail of this vulnerability Click Here (Note :- Registered Member Only- If you are not PlanetCreator.Net Member Sign up Here)
We hope that your security staff will look into this issue and fix it as soon as possible.