Last week, we discussed about vulnerability analysis, exploit writing and being able to circumvent popular exploit mitigation techniques, to drive into it you do need to understand hardware/software/network. If you’re not, you may never be best pen tester!
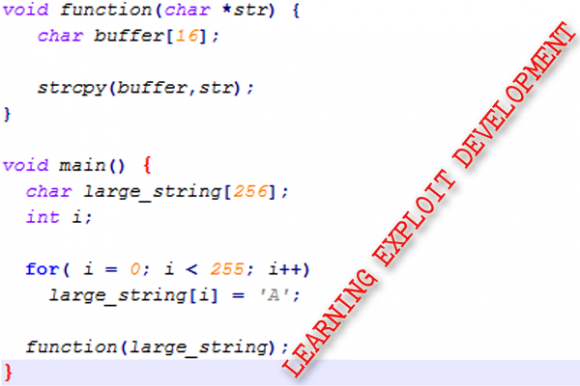
If you are beginner in developing exploits, you still need to learn before trying to do these Stack Corruption, ERI Redirection, Executing Arbitrary Code, SPF Overwrite, Format String Bugs and etc… You can google “Exploiting” tutorials a lot, but I don’t want let your precious time to waste in searching here and there. Now I share Myne-us’s Exploting Development. Sure! You’ll be a master in exploiting development. 😀
Some tutorials do not require assembly language, as my opinion I’m not recommend you to learn it, Step by Step is easy to go’n come!
Good luck!