No man is infallible, Nobody safes @ online and There’s no complete secure protection in this Cyberwar! During these days I’m really busy with my own business! In my dream and my life, I’ld really happy by building Hosting Services but it’s hard to do that kind of business in Myanmar bcoz ISP’s slow and unstable connection! It’s hard to do Own Web Hosting in this Myanmar lol: whatever, I tried to search to some hosting and domain services at malaysia via online…
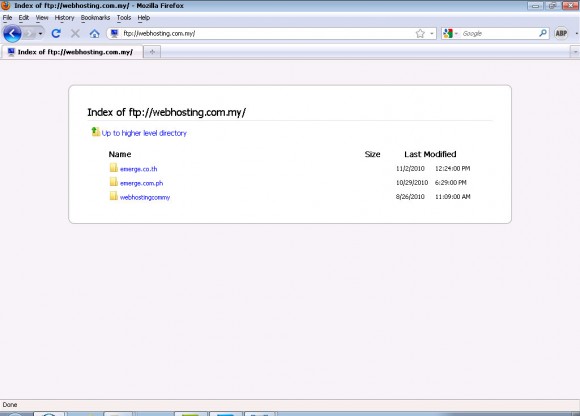
I know this Emerge Web Hosting when I’m working at malaysia, Affordability price, Reliability, Scalability and Rich features. But I found a big security hole in their web server when I clicked http://www.webhosting.com.my/member/
IIS 7.0 error!
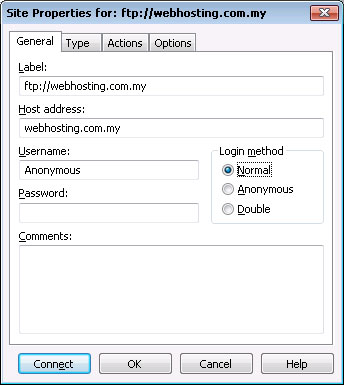
Sure, no secure configuration on their web server!
Everybody can login and crack their server’s web contents,
Hackers can try to upload files, shell and trojan with normal ftp program such as CuteFTP
Ok, tat’all.
I’ll post this in public after they fixed their server. 😀 if not they’ll b xx by Black Hat!
…..
Well, Security Hole has been fixed after had hacked by BurmeseHackers yesterday!. Tat’s why i changed this private post to public!